|
If you suspect that your account has been hijacked (=someone has accessed your login details), you should change your password immediately and inform the security staff at the Office for IT and Digital Infrastructure via abuse@du.se:
While changing passwords, you should create unique passwords for each account, and you should perhaps read Create and use strong passwords.
|
Some ways to recognize a phishing message:
-
Urgent call to action or threats - Be suspicious of emails that claim you must click, call, or open an attachment immediately. Often they'll claim you have to act now to claim a reward or avoid a penalty. Creating a false sense of urgency is a common trick of phishing attacks and scams. They do that so that you won't think about it too much, or consult with a trusted advisor who may warn you away.
Tip: Whenever you see a message calling for immediate action take a moment, pause, and look carefully at the message. Are you sure it's real? Slow down and be safe. -
First time or infrequent senders - While it's not unusual to receive an email from someone for the first time, especially if they are outside your organization, this can be a sign of phishing. When you get an email from somebody you don't recognize, or that Outlook identifies as a new sender, take a moment to examine it extra carefully before you proceed.
-
Spelling and bad grammar - Professional companies or organizations usually have an editorial staff to ensure customers get high-quality, professional content. If an email message has obvious spelling or grammatical errors, it might be a scam. These errors are sometimes the result of awkward translation from a foreign language, and sometimes they're deliberate in an attempt to evade filters that try to block these attacks.
-
Generic greetings - An organization that works with you should know your name and these days it's easy to personalize an email. If the email starts with a generic "Dear sir or madam" that's a warning sign that it might not really be your bank or shopping site.
-
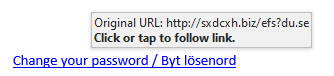
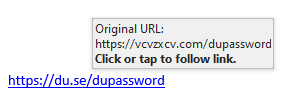
Suspicious links or unexpected attachments - If you suspect that an email message is a scam, don't open any links or attachments that you see. The following example shows links in a message that appears to be from Dalarna University. hover your mouse over, but don't click, the link to see if the address matches the link that was typed in the message. In the following example, resting the mouse on the link reveals the real web address in the box It is clear that the real web address that the link points to is not Dalarna University's URL.
Tip: On Android long-press the link to get a properties page that will reveal the true destination of the link. On iOS do what Apple calls a "Light, long-press". -
Mismatched email domains - If the email claims to be from a reputable company, like Microsoft or your bank, but the email is being sent from another email domain like Yahoo.com, or microsoftsupport.ru it's probably a scam. Also be watchful for very subtle misspellings of the legitimate domain name. Like micros0ft.com where the second "o" has been replaced by a 0, or rnicrosoft.com, where the "m" has been replaced by an "r" and a "n". These are common tricks of scammers.
|
Cybercriminals can also tempt you to visit fake websites with other methods, such as text messages or phone calls. Sophisticated cybercriminals set up call centers to automatically dial or text numbers for potential targets. These messages will often include prompts to get you to enter a PIN number or some other type of personal information. |
If you receive a phishing message
-
Never click on links or attachments in suspicious emails.
If you receive a suspicious message from an organization and are unsure if the message is legitimate, you should contact that organization directly and verify it. Do not reply to the message, but instead launch a web browser and open a new tab. Then go to the organization's website from your own bookmarks or through a web search. There you will find official contact information that you can use to contact the organization. -
If the suspicious message appears to come from a person you know, contact that person via some other means such as text message or phone call to confirm it.
-
Delete the message.
Checklist to protect yourself from phishing and malware
|
IT recommends activation of multi factor login
To increase security and reduce the risk of your user account falling into the wrong hands, you can request that IT activate so-called multifactor login for your user account. Once this has been activated, you will initially have to configure this (see link below) and subsequently, if necessary, confirm your login using your mobile phone (SMS or app). This action significantly increases the security of your user account. To get multifactor login activated, send an email to support@du.se with the heading "activate multifactor on my user account".